Red teaming, the part of offensive security which to most people speaks to their imagination because we test physical, cyber and social defenses all at once.
In this blog post we will go over a red team scenario we executed at the Security Factory and look into which steps led to us compromising a corporate environment.
In this specific example we were hired by a company, let’s call them “Insecorp” (for confidentiality purposes), and the goal of the exercise was to try and see if we could gain access to their network and elevate our privileges without any help from their side.
It was pretty much an “anything goes” scenario, where we were allowed to combine social engineering, phishing, physical intrusions and any technical methods we could think of.

Phishing
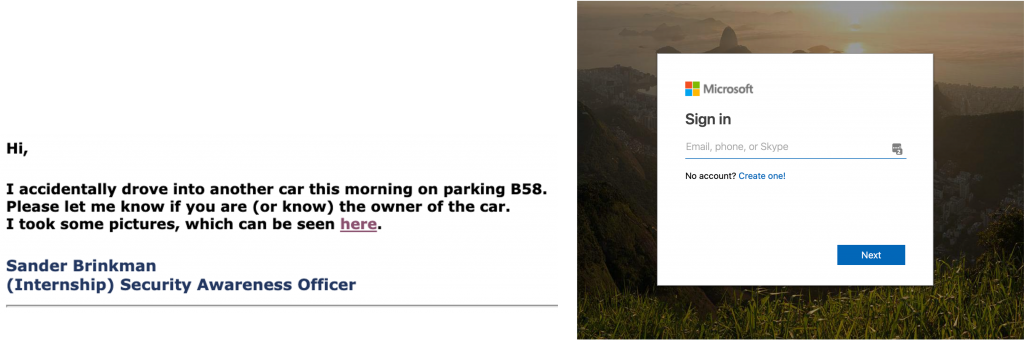
Using the information we obtained in the recon phase, we started creating and sending out a series of phishing mails to employees.
A few mails talked about how someone had crashed into the receiver’s car in the parking lot and required them to click on a link to see the photos, other mails talked about a corporate event that was about to take place and invited them to join it, etc.
Eventually, of the 20 spear phishing mails we sent to them about 15 people had clicked the link and 6 actually entered their account details, leaving us with the domain credentials.
We couldn’t exactly use these credentials to log into any external-facing systems as MFA was required for all employees, however we decided to switch the approach.
The moment of truth (Social engineering)
The day we were going to actually approach the company and physically get our foothold had come.
As we went on site, our social engineer had prepared a plan in case we needed to try and get into the building: he had setup a fake company website for which a shirt and vest had been created and had thought up a full story which would be adapted along the way. This was however the backup plan, and not the main approach we would try first.
We figured that we might be able to use the credentials we captured through phishing to log into the wireless network and get access to the internal network.
This is an approach we have seen work very often and our assumptions paid off, as we connected to the network using an antenna hidden in our car which we parked nearby, we were able to start looking around the internal network and further our attack.
Now a problem appeared however, our car was in the open here… Although most people might not really care about a car parked on the side of the road with the hazard lights on, we did think the physical security guards might eventually catch on if we stayed around for too long.
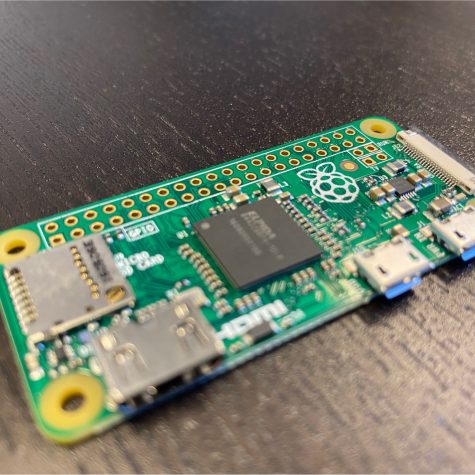
Since the Wi-Fi network was only sufficiently reachable from this specific place we decided to leave behind a small battery-powered Wi-Fi device which could connect back to us over a secondary 4G interface.
We hid the device behind a nearby set of trash cans, verified the connection to the device worked (it did), and left for now.

Compromising the internal network & wrapping up

As we started writing our report, our social engineer went about trying to get into the building the physical way.
Since we had some extra time left due to the speed with which we managed to compromise their internal network, it was decided that having multiple ways in would only benefit them, and the plan had already been written anyway…
The plan worked! Not only did he manage to talk himself into the office building (by using a story about electricity works which needed to be done), he even managed to plug in a new network device we could use as a second potential foothold.
Since he hid it between some cables beneath a desk while posing as an electrician, nobody really questioned it.
As he left, he brought our Wi-Fi device back with him (so it couldn’t be found by some random passer-by) and we informed our contact at the client about the device that was still plugged in into the internal network so their own internal security department could retrieve it.
Conclusion
We managed to compromise the corporate network of “Insecorp” by combining various social engineering techniques with digital security testing techniques compromising a network which, from the outside, looked mostly impenetrable.
With our report and a review meeting afterwards, we managed to give the client some clear advice on how they could improve their overall security and stop a real adversary from doing the same thing.
